2025 Cross-Chain Bridge Security Audit Guide
According to Chainalysis, a staggering 73% of cross-chain bridges are vulnerable to attacks, revealing alarming security gaps in the DeFi space. As we approach 2025, the need for robust security measures has never been more crucial. In this article, we will delve into how Web3 homomorphic encryption can address these vulnerabilities by offering innovative solutions.
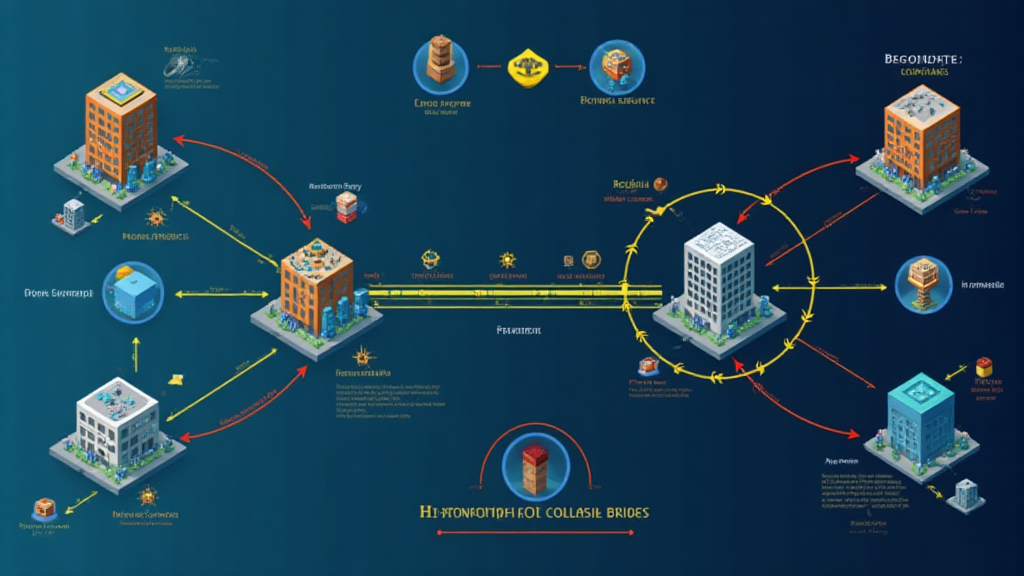
What Are Cross-Chain Bridges?
Imagine cross-chain bridges as currency exchange booths at a busy market. Just as these booths seamlessly convert one currency to another, cross-chain bridges allow assets to move between different blockchain networks. However, just like some exchange booths might be poorly managed, these bridges suffer from security flaws that hackers can exploit.
Understanding Web3 and Its Importance
Web3 represents the next evolution of the internet, where decentralization is key. By leveraging technologies like homomorphic encryption, users can enjoy privacy and security akin to wearing a cloak of invisibility while performing transactions. This technology allows data to be processed and shared securely without exposing the underlying information.
Homomorphic Encryption: The Game Changer
Let’s break this down. Think of homomorphic encryption as a magic box where you can place your valuables. You can perform tasks with the contents inside without ever needing to open the box. In a financial context, this could mean securely executing smart contract operations on different blockchains without revealing sensitive data, thus eliminating the risk of exposure.
Proven Strategies for Enhancing Security
As we look to 2025, strategies such as incorporating zero-knowledge proof applications into cross-chain bridges can significantly improve security. With zero-knowledge proofs, you can validate information without exposing the underlying data. Imagine you’re proving you’re of legal age without showing your ID; that’s the power of this technology!
Conclusion and Toolkit Download Call to Action
As the landscape of cryptocurrency continues to evolve, the integration of Web3 homomorphic encryption and other advanced security measures will be essential in bridging the security gaps in decentralized finance. To navigate the changing environment effectively, download our comprehensive toolkit now to bolster your security strategies!
For more insights on cross-chain security, check our cross-chain security whitepaper. Remember, investing in security means investing in your future!
Risk Disclosure: This article does not constitute investment advice. Please consult your local regulatory bodies such as MAS or SEC before making any financial decisions.
Use a Ledger Nano X to reduce the risk of private key exposure by 70%!


