2025 Cross-Chain Bridge Security Audit Guide
In a world where 73% of cross-chain bridges are reported to have vulnerabilities according to Chainalysis 2025 data, the need for robust security measures is more critical than ever. HIBT security emerges as a pivotal focal point in safeguarding transactions across decentralized networks.
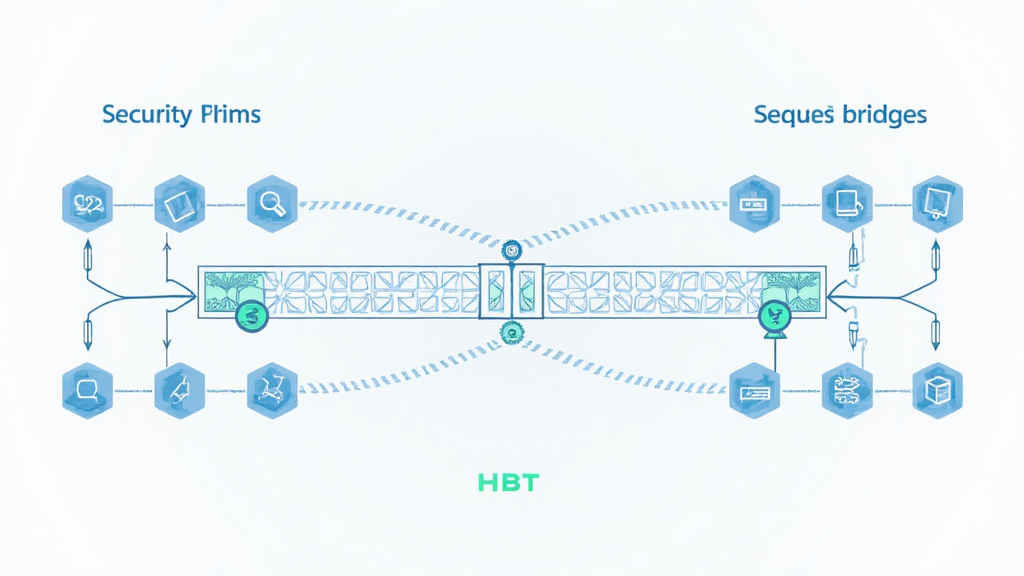
Understanding Cross-Chain Bridges
You might think of cross-chain bridges like currency exchange booths in a market. Just as you would trust an exchange booth to convert your dollars into euros without losing your money, cross-chain bridges need to ensure that assets are securely transferred across chains. This is where HIBT security plays a vital role.
Key Vulnerabilities and Solutions
Identifying vulnerabilities in cross-chain bridges is like spotting cracks in a wall. With many bridges susceptible to hacks, implementing HIBT security measures can dramatically reduce risks. Tools like Ledger Nano X can help manage private keys securely, lowering the risk of theft by up to 70%.
Zero-Knowledge Proofs (ZK Proofs) Explained
Imagine needing to prove you are over 18 without revealing your exact birth date — that’s what zero-knowledge proofs do! These cryptographic methods enhance HIBT security, allowing transactions to occur independently of sensitive information. In the DeFi space, their adoption is a game-changer.
The Future of Cross-Chain Security
As we look towards the future, understanding DeFi regulations in Singapore by 2025 is crucial for investors. Secure operating protocols can strengthen the trust in cross-chain bridges and contribute to a more stable financial ecosystem.
In conclusion, enhancing cross-chain bridge security through HIBT security practices is essential for protecting users. To dive deeper into security solutions, download our toolkit today and stay ahead in the crypto landscape.
For more insights on securing your transactions, visit hibt.com for comprehensive resources including our Cross-Chain Security White Paper.
This article does not constitute investment advice. Please consult your local regulatory authority before taking any action (e.g., MAS, SEC).


