Introduction: The Vulnerability Landscape in 2025
According to Chainalysis data from 2025, a staggering 73% of cross-chain bridges worldwide are vulnerable to attacks, highlighting the pressing need for enhanced security measures. In this article, we will explore HIBT risk management tools that can significantly mitigate these risks.
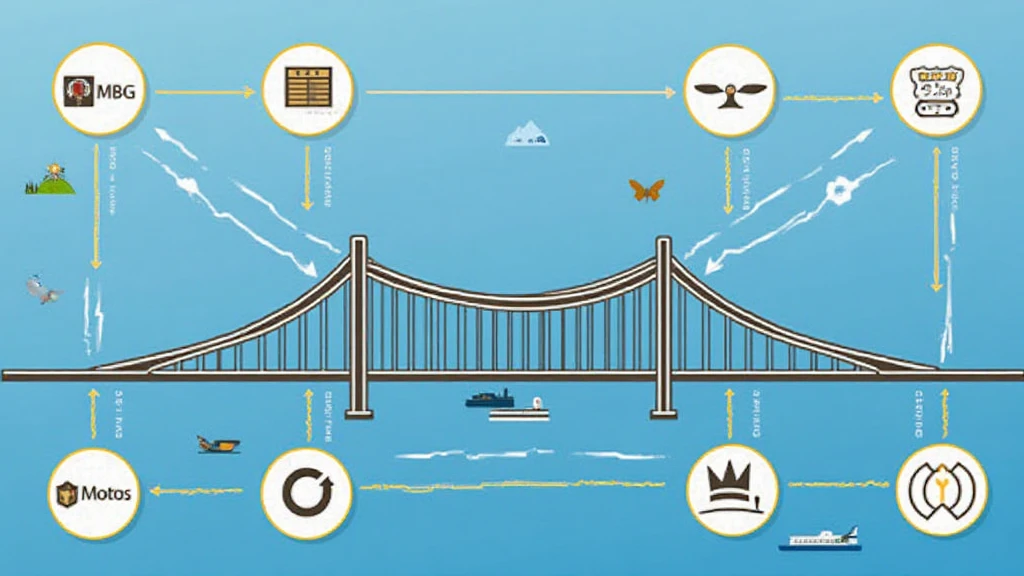
Understanding Cross-Chain Bridges
You might think of cross-chain bridges like currency exchange booths at an airport. Just like you exchange your home currency for local cash, these bridges help transfer assets between different blockchain networks. However, just like not every currency booth is honest, some bridges can expose your digital assets to risks.
Importance of Interoperability
Interoperability is crucial in the blockchain space, allowing different networks to work together seamlessly. It’s like being able to use your phone to buy a snack in different countries without needing to change your payment methods constantly. By implementing HIBT risk management tools, users can achieve better connectivity while safeguarding their transactions.
Zero-Knowledge Proof Applications
Zero-knowledge proofs can be likened to showing a ticket to get into a concert without revealing your personal info. This secure method helps in confirming transactions without disclosing sensitive data, making it a vital tool in risk management for cross-chain operations. HIBT tools leverage this technology for better security.
DeFi Regulation Trends in Singapore
By 2025, the regulatory landscape in regions like Singapore is evolving rapidly. The new regulations in DeFi are aimed at safeguarding investor interests, akin to new traffic laws designed to reduce accidents. It’s essential for users to stay informed about these changes as they can affect transaction processes and security. For comprehensive insights, check out the cross-chain security whitepaper.
Conclusion: Enhancing Security with HIBT Tools
As we conclude, remember the importance of utilizing HIBT risk management tools to navigate the complex landscape of blockchain transactions safely. These tools can significantly reduce vulnerability and ensure that assets remain protected.
For more resources and to download our comprehensive security toolkit, visit hibt.com. Stay informed and secure your digital assets with the right tools!


