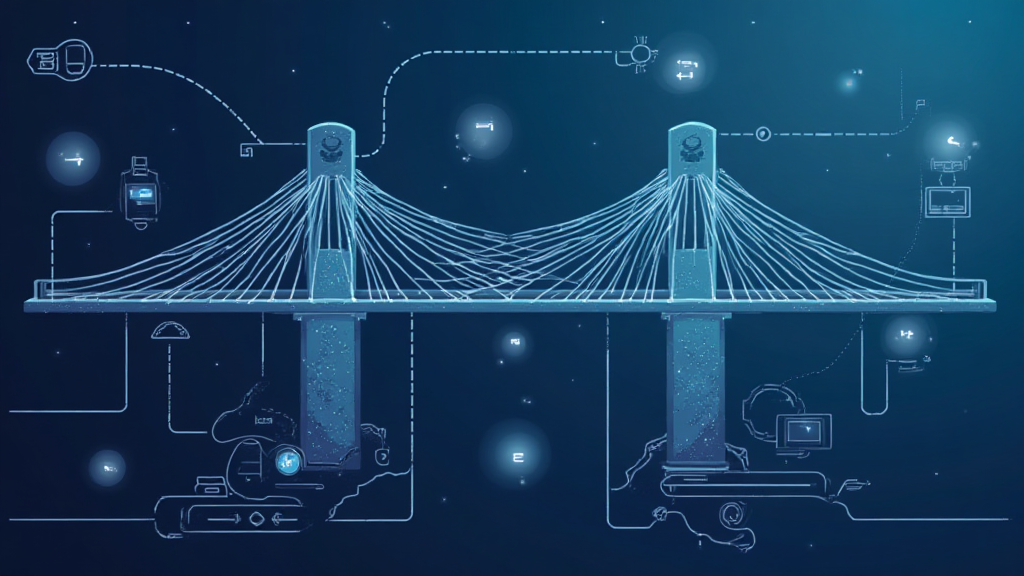
2025 Cross-Chain Bridge Security Audit Guide with HIBT play
As the blockchain landscape evolves, Chainalysis reported that 73% of cross-chain bridges have vulnerabilities. This staggering statistic calls for a deeper understanding of security measures like HIBT play, which incorporates innovations such as cross-chain interoperability and zero-knowledge proof applications.
What Makes Cross-Chain Bridges Vulnerable?
Think of cross-chain bridges like currency exchange booths at your local market. They’re handy, allowing you to swap your dollars for euros, but not all booths are created equal. In the blockchain world, if these bridges are not properly secured, they become hotspots for hacks, leading to significant financial losses.
How Does HIBT play Enhance Security?
Implementing HIBT play in cross-chain protocols is akin to adding security features to your wallet when you travel. Just as you would keep cash in a secure pocket, HIBT play introduces robust mechanisms that protect assets during transfers, dramatically reducing potential vulnerabilities that hackers exploit.
Implications of Zero-Knowledge Proofs in Blockchain
Zero-knowledge proofs are like a magic trick—showing you something without revealing how it’s done. Imagine making a purchase without showing your identifying information; that’s what these proofs achieve. By minimizing data exposure, HIBT play leverages this technology to enhance privacy and security in transactions across various chains.
What’s on the Horizon for Regulatory Trends in DeFi?
As we approach 2025, regulatory landscapes are shifting. New regulations, particularly in hubs such as Singapore, are paving the way for safe and transparent DeFi operations. This means for investors and users, understanding these trends is crucial, as it directly impacts your ability to utilize platforms incorporating HIBT play technologies.
In conclusion, staying informed about the integration of HIBT play in cross-chain infrastructures is essential for both users and developers. It not only addresses the pressing security issues posed by existing vulnerabilities but also enhances overall user confidence as the market matures.
For a comprehensive toolkit on securing your digital assets, download our resources today!
Disclaimer: This article does not constitute investment advice. Consult your local regulatory body (e.g., MAS, SEC) before engaging in cryptocurrency transactions.
Explore more insights on cross-chain security at hibt.com, and don’t forget to check our security white paper for in-depth analysis!
— BitcoinsNewsToday


